How to Manage Crypto as a Team: The Operational Playbook for Funds, Fintechs, and Growing Web3 Businesses
How to Manage Crypto as a Team: The Operational Playbook for Funds, Fintechs, and Growing Web3 Businesses
Summary
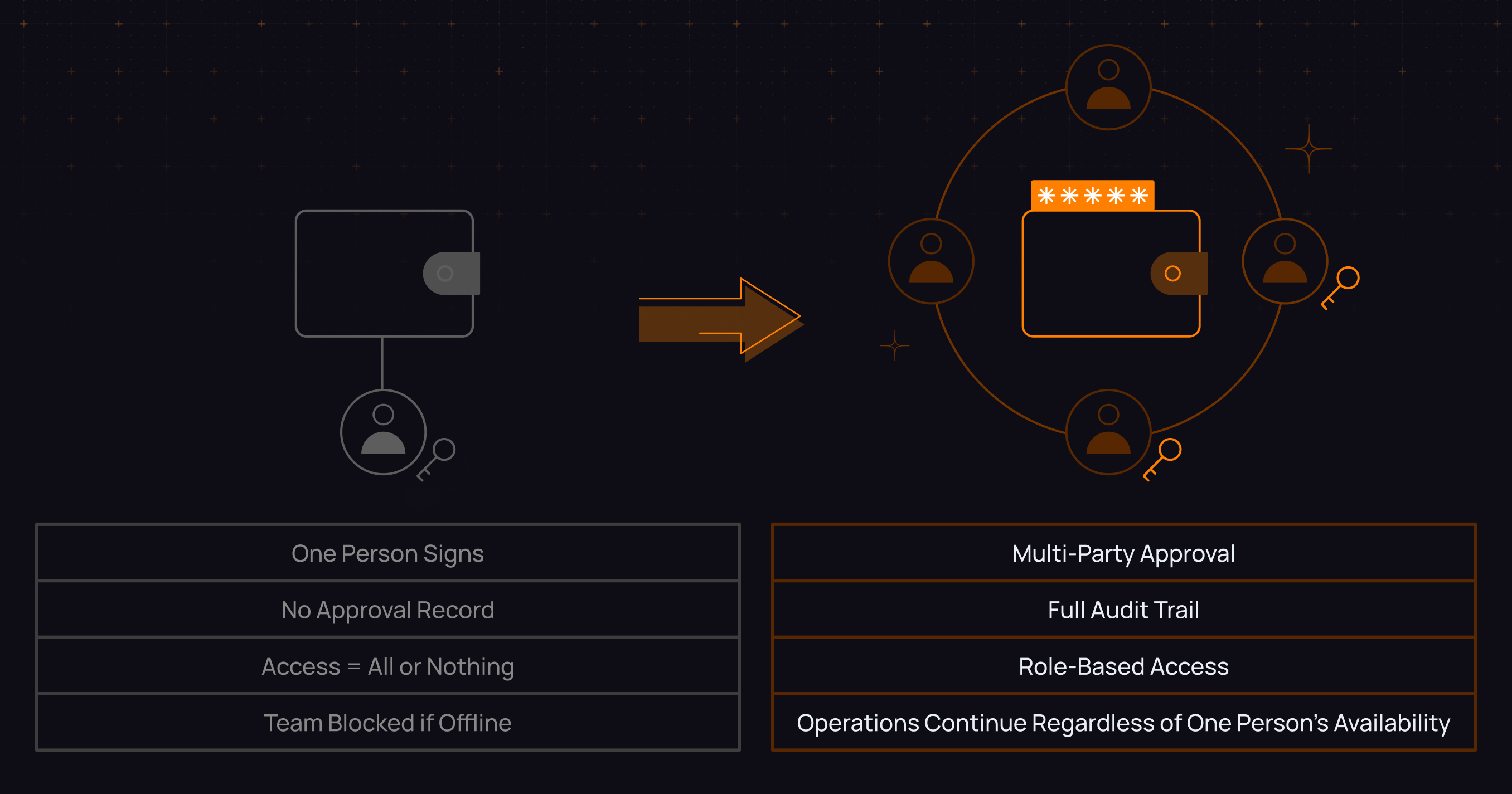
This guide breaks down why personal crypto wallets fail at the team level and what to implement instead. As operations scale across multiple people, wallets, and chains, the real challenge is not security but structure: unclear ownership, lack of approval workflows, poor visibility, and missing audit trails.
It outlines the four core problems every crypto team faces, custody, approvals, visibility, and audit readiness, and provides a practical framework to solve them through role based access, policy driven workflows, and read only multi chain tracking.
The key takeaway: managing digital assets as a team requires more than tools. It requires a system that defines who can act, what they can do, and how every decision is recorded.
Quarter-end chaos isn’t a security failure. It’s a system failure.
Quarter-end. Your investor wants a full breakdown across chains.
Your team is juggling Etherscan, Solscan, a BSC explorer, and a spreadsheet that’s already outdated. The one person who knows where the Arbitrum wallet sits is offline. Somewhere in the mix is a vesting position that may or may not have moved.
No one is sure.
Nothing was hacked. No funds were lost.
The setup just doesn’t work for a team.
The real problem isn’t security. It’s structure.
Tools built for individuals do not translate to teams moving real capital.
Seed phrases do not support approval chains.
Personal wallets do not support roles.
Block explorers do not know your team exists.
This guide is for teams that have already outgrown the personal wallet setup.
Funds, fintechs, family offices, trading desks.
Anywhere “I will ask Dave” is not a system.
Where Solo Wallets Break
Personal wallets were designed for one person. That's not a flaw, it's a design choice. But the moment a second person joins the operation, the gaps start. They just don't announce themselves until something goes wrong.
Here's what those costs actually look like in practice.
Person Dependency: When one person holds the signing keys, the operation depends on that person being available, healthy, reachable, and trustworthy at all times. That person goes on holiday, loses their phone, or leaves the company, and the team either can't move funds or has to scramble to reconstruct access. Neither outcome is acceptable for an operation that moves capital.
No Approval Layer: A personal wallet has no concept of authorization. Whoever holds the keys can initiate and complete a transaction without any review, approval, or context being required. For a trading desk or treasury team, this is not a theoretical problem. It's the reason you can't reconstruct who authorized what three months later when finance needs to close the books.
No Audit Trail: "I think Dave approved it on his phone" is the crypto equivalent of a verbal agreement with no witness. When a regulator asks, an LP demands documentation, or a quarter-end reconciliation doesn't tie out, that answer does not hold up. A wallet that doesn't record who proposed a transaction, who signed it, and under what authorization is not a business tool.
Binary Access: The only settings most personal wallets offer are full access or no access. No middle ground. No read-only for the analyst who needs visibility. No "can initiate but not sign" for the junior ops person. Everyone with access has full access, which means every person added to the operation adds risk in proportion to their permissions, which are always maximum.
Offboarding Risk: When someone leaves the team, what happens to their access? If they had the seed phrase, they have it forever. If they were a signer, rotating that out means a ceremony nobody documented and everyone remembers differently. The clean solution to remove a role, rotate shares, and move on does not exist in a personal wallet model.
None of this is about carelessness. Teams that build on personal wallets do it because that's what exists, not because they haven't thought about it. The model is wrong for the use case. That's a tooling problem, not a discipline problem.
The 4 Problems Every Crypto Team Hits
Every team operating digital assets at scale eventually faces the same four problems. It is worth naming them clearly because each requires a different solution, and solving the wrong problem leads to wasted effort.
1. Custody and control — who actually holds the keys
The custody question sounds like a security question, but it's really an organizational question: as your team grows, who controls access, how is that distributed, and what happens when the distribution needs to change?
Seed phrases concentrate control into a single secret. That secret has to live somewhere, such as a hardware wallet, a piece of paper, or a password manager, and whoever has access to it controls everything. The organizational complexity of a three person trading desk cannot be contained within a twelve word phrase.
Multi-party computation (MPC) solves this structurally. Key material is split across multiple devices and people. No single participant holds enough to act alone. Signing happens through a coordinated computation, not because one person has the full key. The result is that control becomes a property of the team's structure rather than the contents of one person's safe.
2. Approval workflows — how transactions get authorized
Traditional finance has a clear answer to this: the person who requests a payment is not the person who approves it, and the person who approves it is not the person who processes it. These controls exist because they work. They catch errors. They catch fraud. They create an accountability chain that holds up under audit.
Most crypto teams have none of this. Transactions go out because someone decided they should. Maybe they told someone else in Slack. Maybe they didn't. The approval — if it happened — lives in a chat thread that will be impossible to find in six months.
The cost of missing approval logic isn't just compliance risk. It's the operational friction of reconstructing decisions after the fact. Every month-end reconciliation becomes archaeology.
3. Multi-chain visibility — knowing what you actually hold
There's a paradox that good security creates. As teams mature — splitting assets across more addresses, using hardware wallets, rotating cold storage — the portfolio gets safer and simultaneously harder to see. Each address is its own data silo. None of them know about each other. None of them know the team exists.
The result: eight chains, forty wallet addresses, and a spreadsheet that is always at least two weeks behind. Any time someone needs a current position — before a call, before a trade, before a quarterly report — an analyst is spending an hour assembling information that should be available in seconds.
Read-only portfolio tracking across all addresses and all chains, without requiring seed phrase access or wallet connections, is not a luxury feature. It's how teams stay operationally coherent as complexity grows.
4. Audit readiness — proving what happened
The moment of truth looks different each time. Sometimes it's a regulator. Sometimes it's an LP who wants documentation before a capital call. Sometimes it's a quarter-end that doesn't reconcile and finance needs to know why. Sometimes a co-investor disputes a vesting schedule and your team needs to show exactly what moved and when.
The question is always the same: "Who authorized this, when, and under what authority?"
For most teams operating on personal wallets, the honest answer is: the on-chain record exists, but nothing attached to it tells you who decided to make it happen. That gap is not a minor inconvenience. In an environment where the SEC's asset taxonomy is binding and the GENIUS Act's implementing rules take effect in July 2026, teams that cannot produce structured authorization records for their transactions will find compliance reviews expensive and slow.
Roles and Access — How to Structure Who Does What
Translating team hierarchy into wallet access is where most operations either get this right or build a fragile workaround they'll have to undo later.
The underlying principle is simple: in any organization that handles money, not everyone needs the same access. The person who requests a payment is not the same as the person who approves it. The auditor who reviews transactions is not the same as the trader who initiates them. These are distinctions that traditional finance implemented for good reasons, and they apply equally to crypto operations.
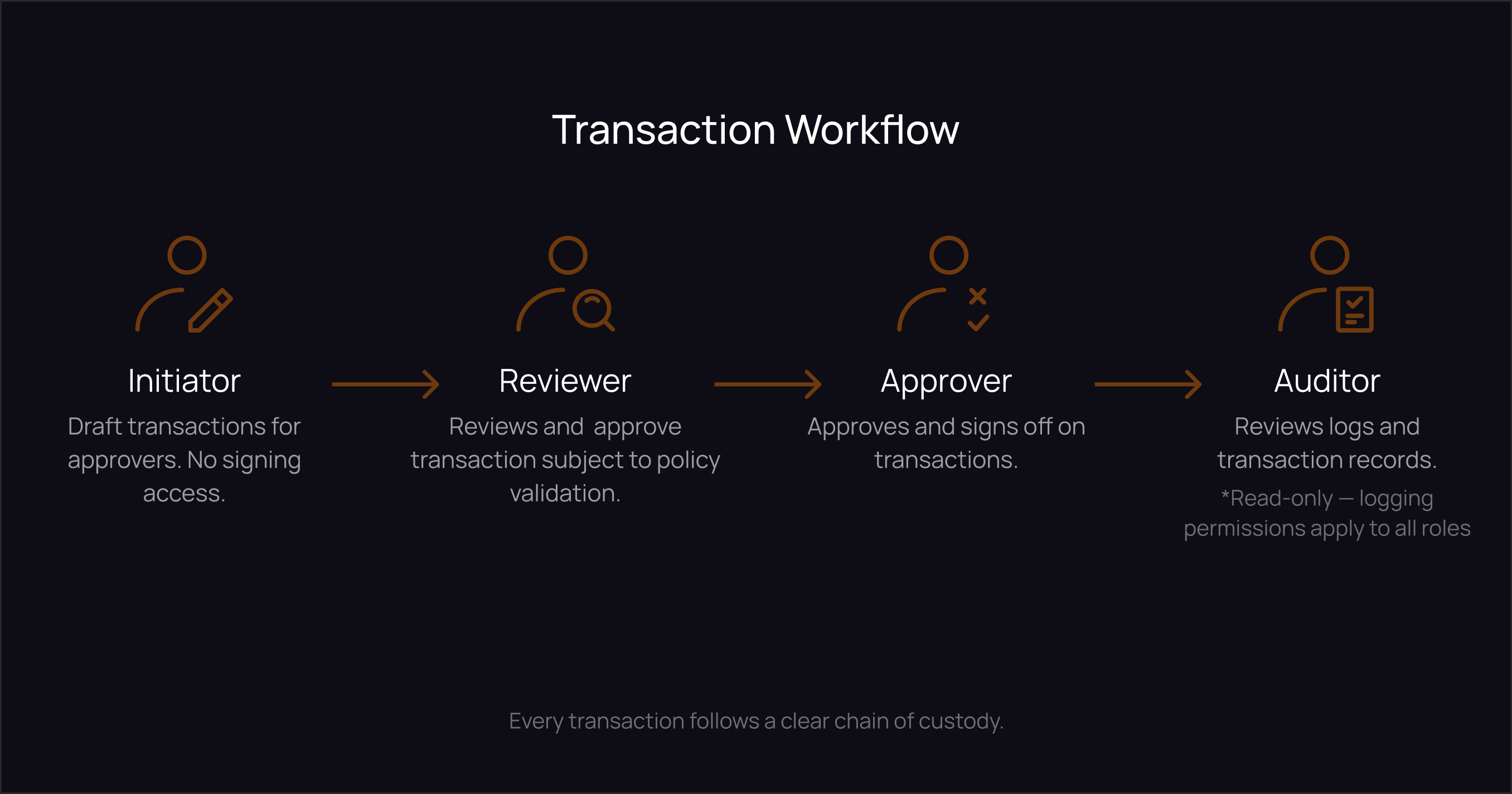
Here's what that looks like in practice across four roles:
Initiator: Proposes a transaction. Selects a destination from the approved address book, specifies the amount and asset, attaches a memo explaining the business purpose. Cannot complete a transaction alone. Cannot sign. The initiation creates a request that moves to the next step — it doesn't move funds.
Reviewer: Checks the context before it reaches the approver. Confirms the destination is correct, the memo is complete, the amount is consistent with what was agreed. This role exists to catch errors before they require a senior approver's attention. In smaller teams, reviewer and approver may be the same person for routine transactions — but the step should still exist in the workflow for anything above a threshold.
Approver: Applies authority to the transaction based on policy rules — amount, destination, chain, time of day — and signs off. Critically, the approver should be able to do this from a mobile device with full context visible. An approval flow that requires the approver to be at a desk, open multiple tools, and reconstruct context that should already be attached to the request will get bypassed in practice.
Auditor (Read-only): Can see everything. Cannot do anything. This role is for finance leads, compliance officers, external auditors, or senior principals who need visibility without operational access. They get the full transaction log, receipts, and activity history. They do not get signing authority.
The distribution of these roles scales with team size:
For a small team of two to five people, start with an owner and co-owner model. Joint control from day one. Both parties need to participate for funds to move. One person's unavailability is an inconvenience, not a crisis.
For a mid-size team of five to twenty people, layer in the full role structure. Traders initiate. Desk leads approve smaller transactions. Finance approves larger ones. The CFO or a compliance lead gets auditor access without signing power.
For larger operations, add step-up approvals for high-value transactions, device-posture checks that verify a signing device meets security requirements, and separation of duties across entities or fund structures.
Offboarding is where this model proves its value. When someone leaves the team, their role is removed. Key shares are rotated. The addresses stay the same. The records stay intact. There is no seed phrase to chase, no shared secret to "change," and no lingering access to worry about.
For a deeper look at how policy-based approvals map to real team structures, the MPC Wallets for Teams: Policy-First Control piece covers the mechanics in detail.
Approval Workflows That Work
The goal of an approval workflow is not to slow things down. It's to route friction to where risk actually lives, and keep everything else fast.
A well-designed approval workflow turns judgment calls into repeatable, predictable flows. The approver shouldn't have to figure out whether a transaction is acceptable. The policy does that work. The approver confirms that the policy fired correctly and the context is what they expect.
What a policy covers:
A transaction policy is a set of rules that determines how a specific category of transaction should be handled , including who approves it, what limits apply, and what documentation is required. A good policy is short enough to fit in a paragraph, clear enough that a new team member can understand it in two minutes, and specific enough to be testable.
Key policy fields:
- Amount Thresholds: Small transactions route to a desk lead. Above a set amount, finance approval is required. Above a higher threshold, a second approver or a time-hold applies.
- Time Windows: Large outflows are restricted to business hours. Weekend or after-hours transactions for above-threshold amounts require an exception code.
- Destination Rules: All payouts go to addresses in the approved whitelist. New payees require dual review before the first transaction is authorized. The whitelist uses contract IDs, not ticker symbols. USDT on Ethereum and USDT on Tron are different assets, and the policy should treat them as such.
- Chain-specific Routing: Vendor payouts default to BSC or Tron for fee predictability. Ethereum is available when specifically required by the counterparty. This isn't a preference but a policy rule that prevents a team member from defaulting to the most expensive chain out of habit.
- Memo requirements: Every transaction requires a business context note. This is not administrative overhead. It is the difference between an audit trail and a list of on-chain events with no context.
Three policy templates that cover most of what a team needs:
- Routine Vendor Payout: Amount cap per transaction, BSC or Tron preferred, destination locked to the vendor whitelist, memo required. Desk lead approves. Finance approves anything above the cap.
- Treasury Top-up: Weekly cap, business hours only, fee ceiling on Ethereum, destination restricted to whitelisted exchange accounts or cold storage. Finance approval required.
Visibility Across Wallets and Chains — The Other Half of Control
Here is something that catches teams off guard: the better your security habits, the worse your visibility gets.
The security-conscious operator splits assets across multiple addresses to reduce blast radius. Uses cold storage for long-term holdings. Operates separate wallets for different fund entities or strategies. Rotates addresses. All of this is correct. All of this is what serious teams are supposed to do.
It also means the portfolio is now spread across eight chains, forty wallet addresses, and no native way to see all of it at once.
High-value exception: Senior multi-party approval, minimum 30-minute hold before execution, reason code required, both transaction hashes captured on the receipt if a bridge is involved.
One operational rule worth stating plainly: keep bridges off by default. When liquidity genuinely needs to move across chains, require a reason code and capture both transaction hashes. Bridge exploits have caused losses in the hundreds of millions across the industry. Extra steps on bridging transactions are not bureaucracy — they're a reasonable reflection of the risk involved.
QoreWallet's policy engine is built around exactly this model. Thresholds, destination rules, time windows, and memo requirements are configured once and enforced across every transaction — regardless of which chain the transaction touches. The control layer doesn't change when the chain changes.
Every time someone needs a current position — before a call, before a trade, before a quarterly report to LPs — an analyst is opening browser tabs. Etherscan. Solscan. The relevant layer-2 explorer. Cross-referencing a spreadsheet that may or may not reflect the current state of a vesting contract that unlocked last Tuesday.
This is not a discipline failure. It's a tooling gap. The addresses do not know each other. They do not know the team exists. Each one is a data silo, and assembling them into a coherent picture requires human effort every single time.
The security paradox matters here. As operations mature and security improves, visibility degrades. The teams with the strongest custody practices often have the weakest operational visibility. Fixing this requires tracking that doesn't compromise the custody posture it's meant to complement.
Which means: a tracking tool should never ask for a seed phrase, private key, or wallet connection. The moment it does, it has introduced a new attack surface — a system that holds credentials to every address the team watches. That's not a monitoring tool. That's a target.
The rational model is read-only tracking: add a public wallet address, get full visibility into balances and activity, with no signing capability introduced. The tool observes. It does not touch.
What proper tracking gives a team:
A consolidated view across all addresses and chains — not per-chain dashboards, not per-wallet snapshots, but a single live picture that aggregates automatically. When a position moves, the team sees it without running a query.
Real-time activity, not reconstructed history. The question "did anything move since last week that we didn't expect?" should take ten seconds, not an hour.
Clean reporting output. When an LP asks for a portfolio update, the data should already be organized. Producing a report should be an output of the tracking system, not a separate project that requires pulling from five tools and reconciling differences.
QoreWallet handles the custody and control side — who signs, under what authority, within what policy constraints. QoreDAM handles the visibility side — what the team holds, across every address and chain, in real time. The two problems are distinct. They need distinct solutions. And they are most useful when they run together: QoreDAM surfaces the position; QoreWallet governs the action.
Running only one of them leaves a gap. Visibility without control means the team can see everything but cannot govern who acts on it. Control without visibility means transactions are well-governed but the team doesn't have a reliable picture of what they're governing. The full operational picture requires both.
For a deeper look at the tracking problem specifically, Track Multiple Crypto Wallets covers the VC and fund use case in detail. The Multi-Chain Reality Check covers why good security habits create visibility gaps.
See the Stop Running a Rescue Operation piece for a full 90-day implementation plan, including a tabletop drill for lost-device scenarios.
Audit Trails and Compliance Readiness — What "Proof" Actually Looks Like
An audit trail is not a dashboard. It is evidence. The distinction matters because dashboards show current state; evidence proves historical decisions.
When a regulator asks who authorized a specific transaction, when, and under what authority — a chart of portfolio performance doesn't answer that question. A structured transaction receipt does.
Here's what every transaction record should contain:
- Initiator identity and timestamp who proposed the transaction and when
- Reviewer identity and timestamp who checked it before it reached the approver
- Approver identity and the policy that fired who approved it, and which policy rule authorized the action
- Asset, chain, and exact contract address with correct decimals. Not "USDT." USDT on BSC, contract address included.
- Destination label from the address book, plus the raw address the human-readable label and the on-chain address, both captured
- Memo the business context attached at initiation
- On-chain transaction hash and block explorer link the immutable record
- Fee amount and fee asset so reconciliation and tax treatment don't require separate reconstruction
The standard worth holding to: pull any random transaction from six months ago. Within 60 seconds, you should be able to answer who proposed it, who approved it, what policy authorized the action, and what the business reason was. If that answer takes longer than 60 seconds, a field is missing.
On the regulatory environment: the GENIUS Act's implementing rules take effect in July 2026. The SEC and CFTC issued a binding five-part asset taxonomy in March. Both developments point the same way — toward structured documentation, formal classification records, and auditable transaction histories. Teams that arrive at compliance reviews with Slack threads and CSV exports cobbled together from block explorers will spend significantly more time and money than teams that have been capturing structured receipts from the beginning.
This is not about anticipating the worst case. It's about recognizing that the cost of structured record-keeping is low, and the cost of reconstructing it after the fact is high.
Receipts should export in a format finance can use directly — one CSV, all chains, consistent column structure. The receipt is not a crypto artifact. It is a financial document.
The At Its Qore — March 2026 newsletter covers the SEC taxonomy and the Resolv breach — a $25 million loss that came not from a smart contract exploit, but from a compromised cloud key management system.
What the Operational Stack Looks Like When It's Working
Pull back and look at what the previous four sections are actually describing. They're three distinct problems with a common shape.
Control: who can act, and under what authority. This is the roles, MPC signing, and the policy engine — the layer that determines whether a transaction happens at all, and who bears responsibility for it when it does.
Visibility: what you actually hold. The consolidated dashboard across all addresses and chains. Real-time activity without manual assembly. The picture that exists before someone asks for it, not the one built in response to the question.
Evidence: what happened and why. Structured receipts that capture every decision — who proposed it, who approved it, which policy governed the action, what the business context was, and what the on-chain outcome was.
These aren't three separate workstreams. They are one stack, and it fails in the direction of the weakest layer. Good visibility without control means anyone can look but nobody is governing. Good control without visibility means transactions are well-governed but the team doesn't actually know what it's governing. Both without structured evidence means the governance can't be demonstrated after the fact — which is exactly what compliance, audit, and LP reporting require.
Running all three is not an enterprise-only proposition. It's the operational baseline for any team that is past the personal wallet stage and plans to stay there. The difference between a team that can answer a regulator's question in an hour and one that needs a week to reconstruct the same answer is usually just this stack, properly implemented.
Where to Start If You're Building This From Scratch
The temptation is to fix everything at once. Resist it. The teams that do this well start with roles, get those right, and build everything else from that foundation.
Week 1: Define your roles. Write down who initiates, who reviews, who approves, and who gets read-only access. Do this for your current team, at its current size. This document is the operational blueprint that everything else references. It doesn't need to be complex — a clear list of names, roles, and permissions is enough to start.
Week 2: Build your address book. Every wallet address your team interacts with — exchanges, vendors, treasury wallets, cold storage addresses — goes into a single list. Label each one clearly. Add contract IDs for assets where the chain matters. Remove anything stale. The address book is the foundation of destination rules in your approval policies.
Week 3: Write three core policies. A routine vendor payout policy. A treasury movement policy. A high-value exception policy. Keep each one short — it should fit in a paragraph. Run a tabletop exercise on each: "A transaction comes in that matches this policy. Walk through what happens." If anyone is unclear on a step, the policy needs more specificity.
Week 4: Connect your tracking. Add every address your team owns or monitors to a read-only dashboard. Get the consolidated view. Confirm that the picture matches your expectations. Flag anything that doesn't.
After those four weeks, you have the foundation of a serious operation: defined roles, a clean address book, tested policies, and real-time visibility across your full position. Everything that follows — more sophisticated policy rules, deeper chain coverage, integration with ERP and accounting systems — scales from that base.