Qore3's "At Its Qore" — March 2026 Edition
Qore3's "At Its Qore" — March 2026 Edition
March 30, 2026
Welcome back to At Its Qore. Each month, this newsletter filters the noise into three operator-critical lanes: Technology & Protocols, Regulation & Policy, and Security & Incidents. The goal stays the same: understand what changed, why it matters to real teams, and what control should ship next.
[TLDR]
- What changed: The SEC and CFTC jointly issued the first binding crypto asset taxonomy; Solana's community approved its P-Token standard for mainnet deployment; a $25 million DeFi breach happened via a compromised AWS key — not a smart contract bug.
- Why it matters: Regulatory clarity has arrived with formal weight — every asset in your stack now sits in a legal category whether your team has mapped it or not. Infrastructure upgrades are reshaping on-chain cost assumptions ahead of schedule. And attackers have fully pivoted from code exploits to cloud key management, the quietest single point of failure in most stacks.
- What to do next: Run an asset classification audit against the new five-part taxonomy before the formal rulemaking lands. Update your token throughput model for a post-P-token environment. Enumerate and harden every cloud-managed key that touches protocol operations.
1) Technology & Protocols
Article: Solana Approves P-Token Standard for Mainnet (openPR, March 2026) [1]
Operator impact: Token operation costs, batch sizing, and throughput planning will shift materially when P-tokens land — teams still running on SPL Token assumptions are pricing their infrastructure on numbers that are about to become outdated.
Key takeaway: Solana's community approved SIMD-0266, which introduces the P-token standard — a compute-optimised, drop-in replacement for the existing SPL Token program. The efficiency gain is significant: token operations are projected to use up to 95–98% fewer compute units, freeing roughly 12% of network block space across the board. Critically, P-tokens are fully backward compatible, meaning existing client code continues to work without modification. The standard is currently on testnet, with mainnet deployment expected in H2 2026. The underlying architecture relies on zero-copy data access and no heap allocation — technical choices that make every token transfer faster and cheaper without requiring protocol rewrites from developers. For teams building or managing token-heavy operations on Solana — stablecoin flows, treasury management, DeFi integrations — this is not a marginal optimisation. It is a structural shift in how compute capacity is priced and consumed on the network.
One control to add: A "Token Throughput Baseline" review. Before P-tokens reach mainnet, document your current compute unit (CU) budgets for key token operations: transfers, batch settlements, approvals. Then run a forward projection: if CU costs drop by 95%, what does that mean for your batch sizing strategy, your fee reserves, and your settlement timing assumptions? Assign a protocol owner to track testnet performance metrics and define a "migration readiness" flag — a specific trigger point that fires when mainnet activation becomes imminent, so the team is not scrambling to recalibrate in real time.
2) Regulation & Policy
Article: SEC and CFTC Issue Landmark Joint Interpretation on Crypto Asset Classification (CoinDesk, March 17, 2026) [2]
Operator impact: Every digital asset your team holds, transacts, or integrates now has a regulatory category attached to it — and the agencies have made clear they will act on that taxonomy. The question is whether your classification register exists before enforcement asks the same question.
Key takeaway: On March 17, the SEC and CFTC jointly issued the first commission-level binding interpretation of how federal securities laws apply to crypto assets. The guidance establishes a five-part taxonomy: digital commodities, digital collectibles, digital tools, stablecoins, and digital securities. Eighteen major cryptocurrencies were explicitly identified as digital commodities. Airdrops, protocol staking, and protocol mining received explicit regulatory treatment — most falling outside securities classification under defined conditions. This is not staff guidance. It carries formal agency weight, and both chairs signed it. SEC Chairman Atkins called it the end of "more than a decade of uncertainty," while CFTC Chairman Selig positioned it as the start of harmonised federal oversight. A formal rulemaking — expected to exceed 400 pages — was signalled for release within weeks and will carry further detail on an "innovation exemption" for crypto firms. The CLARITY Act continues its Senate journey in parallel, meaning the regulatory floor may move again before year end.
One control to add: An "Asset Classification Audit." Map every digital asset your team holds, transacts, or integrates against the new five-part taxonomy. Flag anything that lands in "digital securities" territory — those carry the heaviest compliance obligation. Assign legal sign-off per asset classification, and build a 30-day review cadence into the workflow, because the formal 400-page rulemaking that follows this interpretation may shift classifications for specific instruments. Do not wait for that rule to arrive before running the first pass. Teams that already know where every asset sits will move faster when the next update drops.
3) Security & Incidents
Article: DeFi Losses Hit $137M in Q1 2026 as Resolv Hack Adds to Growing Exploit Toll (CoinGenius, March 25, 2026) [3]
Operator impact: If your protocol's key management runs through a cloud provider, the attacker's target is no longer your smart contract — it is your cloud console. The smart contract can be airtight and still not save you.
Key takeaway: On March 22, the Resolv protocol was drained of more than $25 million after an attacker compromised an AWS Key Management Service (KMS) key controlling critical protocol operations. The smart contracts were not the entry point. The cloud infrastructure around them was. Security researcher Rekt News observed that "DeFi protocols are only as secure as their weakest infrastructure component. When key management is centralised through cloud providers, it creates a single point of failure that undermines the entire decentralised architecture." This is a continuation of the structural shift that defined 2025 crypto losses: infrastructure attacks — compromises of keys, wallets, and control planes — drove 76% of all stolen funds across that year, averaging $48.5 million per incident. Code exploits are declining. Cloud access failures are rising. The Resolv breach is a clean case study in why: the decentralised protocol held its ground while the centralised key management layer it depended on did not.
One control to add: A "Cloud Key Audit." Enumerate every AWS KMS key, Google Cloud KMS credential, or equivalent cloud-managed secret that touches your protocol operations. For each key: Who has IAM console access? When was access last reviewed? Is there a multi-party approval requirement before the key is used? Is there anomaly monitoring on key usage — unusual times, volumes, or geographies? Then run a quarterly tabletop: "Cloud console compromised at 2am on a Friday. What happens next?" The metrics that matter are time-to-detection and time-to-revocation. Target both under fifteen minutes. If either number is currently unknown, that is the gap to close first.
Expert Corner: The Permission Stack
March's three stories are not separate events. They are one mechanism running in sequence.
Solana approves P-tokens and unlocks a significant increase in network capacity — cheaper operations, more block space, faster throughput. Regulatory taxonomy arrives the same month and assigns legal permission to every asset on every chain — some get a lighter touch, some get the full securities weight. Then an attacker walks into Resolv through an AWS key that nobody had hardened and takes $25 million without touching a line of smart contract code.
Chain reaction: As the rails become more capable, more value moves on-chain. As regulatory categories firm up, more institutions feel safe enough to move that value in scale. As institutional volume grows, attackers shift their targeting from "find the bug in the code" to "find the key in the cloud." The attack surface does not disappear with better infrastructure — it moves up the stack to wherever governance is weakest.
Who benefits and who gets squeezed: Teams that maintain what you might call the Permission Stack win on three dimensions simultaneously. Regulatory taxonomy gives legal permission to operate. Infrastructure upgrades give technical permission to scale. Proper key governance prevents attackers from getting operational permission to take it all away. Every team missing one of those three layers is carrying risk that March's headlines just made visible.
March's concept: The Permission Stack. Legal clarity, infrastructure capacity, and key-level access control are not three separate workstreams. They are one stack. Regulators just defined the bottom layer. Engineers are optimising the middle. Attackers are already probing the top. The teams that will move fastest in Q2 are the ones who treated all three as a single control surface.
Further Reading: The Q1 2026 Recap That Goes Beyond the Price Chart
March is also when Qore3 published its full Q1 2026 industry recap — and it makes a direct companion to this edition.
The short version: Bitcoin logged its worst-ever start to a financial year. Billions left spot ETFs. The Fear & Greed Index hit 19. On the surface, Q1 looked like a setback.
It was not. It was a filter.
While the charts bled, regulation got signed into law, institutional money paused and then came back, and the infrastructure conversation that serious digital asset teams need to be having stopped being niche. The GENIUS Act is already on the books. Hong Kong is issuing its first stablecoin licenses. The strategic Bitcoin reserve is a sovereign-level statement. Real-world asset tokenization kept building through the noise.
The article's central argument is one that every operator should keep close: the teams that struggled most in Q1 were not the ones who failed to predict the pullback. They were the ones who had no operational infrastructure to fall back on when conditions got difficult. Shared seed phrases. Manual reporting. No audit trail. Approval workflows held together by WhatsApp threads. Market stress did not create those problems. It just made them visible.
The full breakdown — all five Q1 themes plus a Q2 outlook — is on the Qore3 blog.
Read: Tariffs, ETF Swings, and Stablecoin Laws: Everything That Moved Crypto in Q1 2026
Stop Running Digital Asset Operations on Improvisation. There Is No Excuse Anymore.
Q1 did not break teams because the market pulled back. It broke teams because they had no infrastructure to fall back on when it did. That is a different problem — and it has a direct answer.
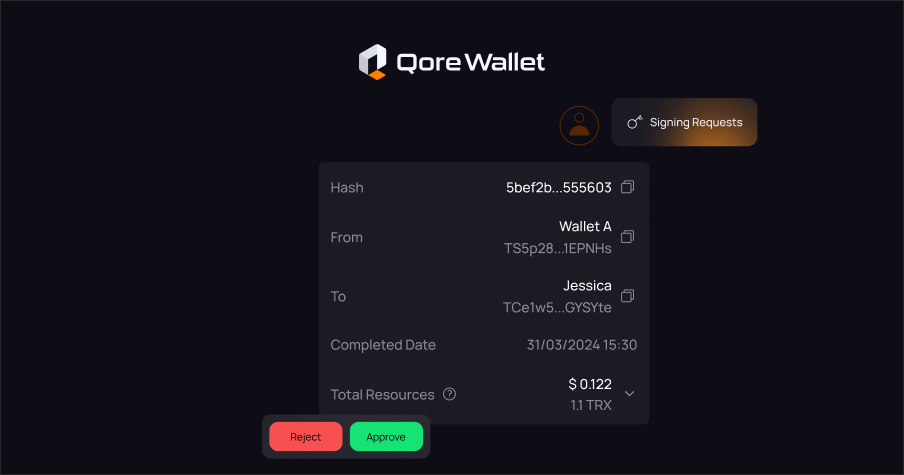
QoreWallet: Control that does not depend on one person.
Right now, somewhere on your team, one person holds too much. One key. One device. One set of permissions that nobody formally agreed on. That person goes offline, makes a mistake, or gets targeted — and your entire operation is exposed. QoreWallet ends that.
Every transaction requires the right people to sign off before it moves. Role-based permissions lock each team member to exactly what they need — and nothing beyond it. MPC technology splits signing authority across the team so no single individual, device, or credential can act alone. Every approval, every rejection, every action is timestamped and logged — permanently. When something goes wrong, or when a regulator asks, the answer is not "I think it was Dave." It is a complete, structured record.
That is not a security feature. That is how serious operations run.
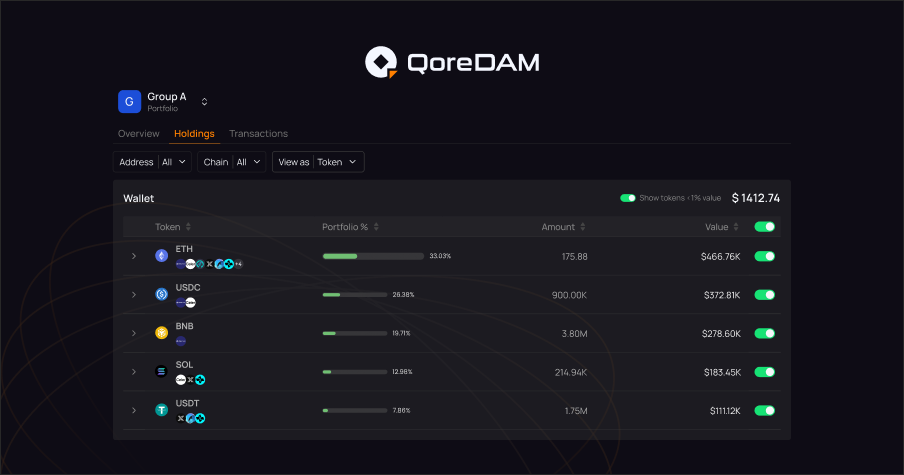
QoreDAM: Visibility that does not require a spreadsheet rebuild every Monday.
Your assets do not sit in one place. They never did. Multiple wallets, multiple addresses, multiple chains — and every time someone needs a position update, someone else is opening browser tabs, cross-referencing block explorers, and manually reconciling numbers that were already stale by the time they were written down.
QoreDAM connects every wallet and every chain into one live dashboard. Activity surfaces in real time. Flows are traceable without exports. Portfolio positions are current, not reconstructed. The answer to "where do we stand right now?" stops being a thirty-minute project and becomes a ten-second glance.
One stack. Two products. Zero excuses for operating blind.
Here is the honest version: QoreWallet without QoreDAM means you govern what moves but cannot see the full picture you are governing. QoreDAM without QoreWallet means you can see everything but cannot control who acts on it. Either half alone leaves a gap that Q1 — and the Resolv breach, and the new SEC taxonomy — just made more expensive to carry.
Together, QoreDAM surfaces the position. QoreWallet governs the action. Every decision your team makes is grounded in real data and executed through a controlled, auditable workflow. That is the operational standard that serious digital asset teams are moving toward in 2026. The ones that get there first are not going to wait for the next incident to make the case for them.
QoreWallet — Get your team set up QoreDAM — Join the waitlist
March's Wrap-up
March arrived with more regulatory clarity than the industry has seen in a decade — and an incident that reminded everyone what happens when teams conflate "decentralised protocol" with "no cloud dependencies." Those two things can coexist in the same stack, and they often do. The Resolv breach is the proof.
What to watch in April: The SEC's formal 400-page rulemaking that follows the March 17 interpretation — classification details will shift further; any official Alpenglow mainnet activation timeline from the Solana team; and whether the Resolv breach triggers a wave of cloud key audits across DeFi or gets quietly archived as "a Resolv problem."
What's coming from Qore3: QoreWallet. Built for the team that cannot afford one person, one key, and no audit trail. Role-based access. Approval workflows. MPC signing. The operational layer that should have shipped before your last incident.
References
[1] Solana (SOL) Approves P-Token Standard for Mainnet. (2026, March). openPR / CoinMarketCap. https://www.openpr.com/news/4431979/solana-sol-approves-p-token-standard-for-mainnet-while-taurox
[2] U.S. SEC Issues First-Ever Definitions for What Crypto Assets Are Securities. (2026, March 17). CoinDesk. https://www.coindesk.com/policy/2026/03/17/u-s-sec-issues-first-ever-definitions-for-what-crypto-assets-are-securities / SEC Press Release No. 2026-30. https://www.sec.gov/newsroom/press-releases/2026-30-sec-clarifies-application-federal-securities-laws-crypto-assets
[3] DeFi Losses Hit $137M in Q1 2026 as Resolv Hack Adds to Growing Exploit Toll. (2026, March 25). CoinGenius. https://coingenius.news/defi-losses-137m-q1-2026-resolv-hack-exploit/